
Karma-X Blog
The Quantum Trojan Horse: Can We Trust the Next Generation of Cryptography?
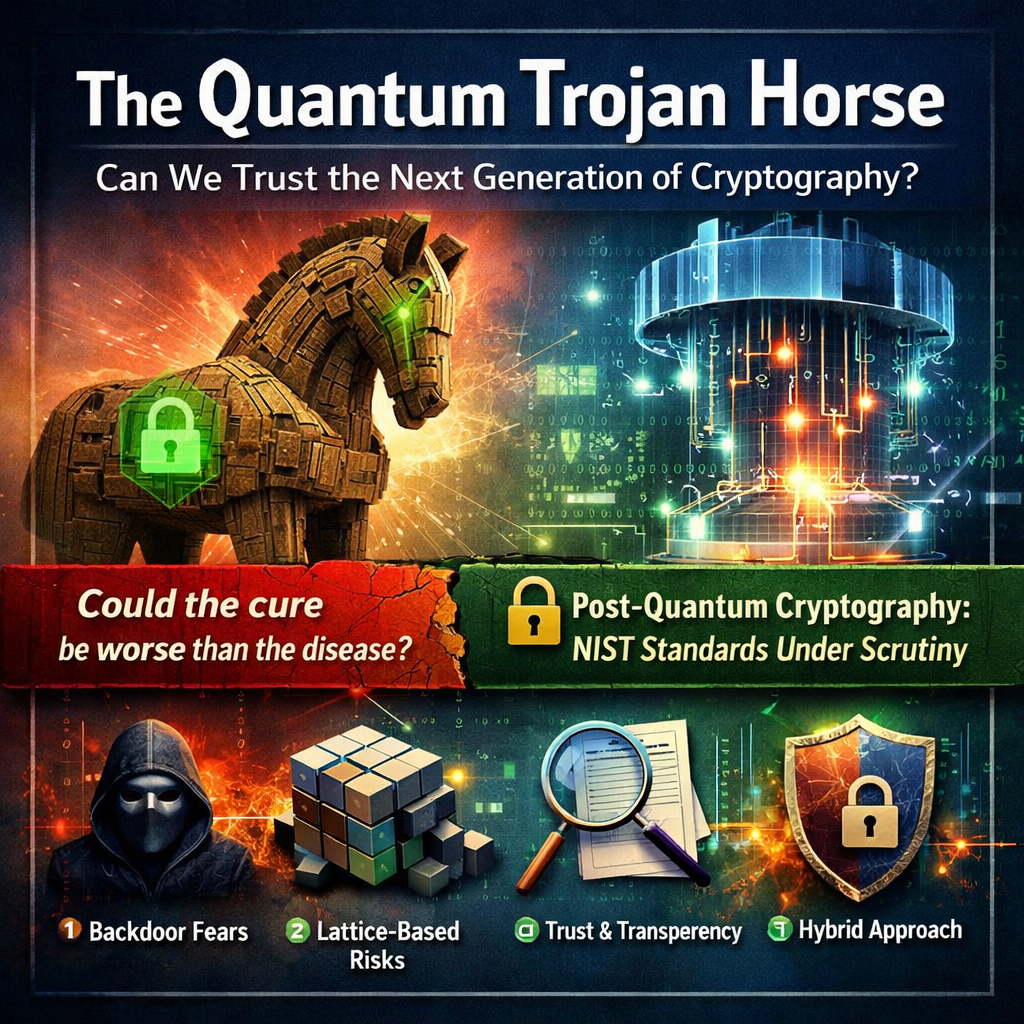
The world is racing to replace its cryptographic infrastructure before quantum computers render it obsolete. But in the rush to adopt new standards, we must ask a question the cryptographic community has been burned by before: Could the cure be worse than the disease?
The world is racing to replace its cryptographic infrastructure before quantum computers render it obsolete. But in the rush to adopt new standards, we must ask a question the cryptographic community has been burned by before: could the cure be worse than the disease?
Post-quantum cryptographic (PQC) algorithms are being standardized right now by NIST. These will protect everything from banking transactions to classified military communications. History tells us that standardization processes are precisely where intelligence agencies have inserted backdoors before. Are we walking into the same trap?
Quantum computers exploit principles of superposition and entanglement to solve certain mathematical problems exponentially faster than classical machines. The specific threat to cryptography comes from Shor's algorithm, which can efficiently factor large integers and compute discrete logarithms—the two hard problems that underpin...
This is premium content from our research team. Create a free account to access the full article and join our community of security professionals.
Already have an account? Sign in here
The Bottom Line: The world is rushing to adopt new encryption algorithms that can resist quantum computers. But history shows us that the standardization process itself—the part where governments decide which encryption everyone uses—is exactly where backdoors have been inserted before. We need to ask hard questions before we trust the next generation of cryptography with everything.
Quantum computers are coming, and when they're powerful enough, they'll be able to break the encryption that protects virtually everything online—your bank account, your emails, military secrets, medical records, all of it.
To prepare, governments and companies are racing to adopt new "post-quantum" encryption algorithms. In August 2024, NIST (the US agency that sets cryptographic standards) released the first set of these new standards. Everyone is being told to start switching over immediately.
The question is: can we trust these new standards?
Here's why the cryptographic community is nervous. In the 2000s, NIST standardized an encryption component called Dual_EC_DRBG. It turned out to have a backdoor built in by the NSA.
Create a free account to read the complete article and access our full library of research content.
From small business to enterprise, Karma-X installs simply and immediately adds peace of mind
Karma-X doesn't interfere with other software, only malware and exploits, due to its unique design.
Whether adversary nation or criminal actors, Karma-X significantly reduces exploitation risk of any organization
Update to deploy new defensive techniques to suit your organization's needs as they are offered